Personal data stored with digital service providers is the primary attack zone for cyber criminals in this digital age. We are in the era of digital warfare. The post-pandemic era has initiated the move to have businesses provide almost all services online and the authentication component has become an essential element in the design of digital services.

Organisations and businesses have realised that digital security is the top/highest priority and investment in this space cannot/should not be easily neglected.
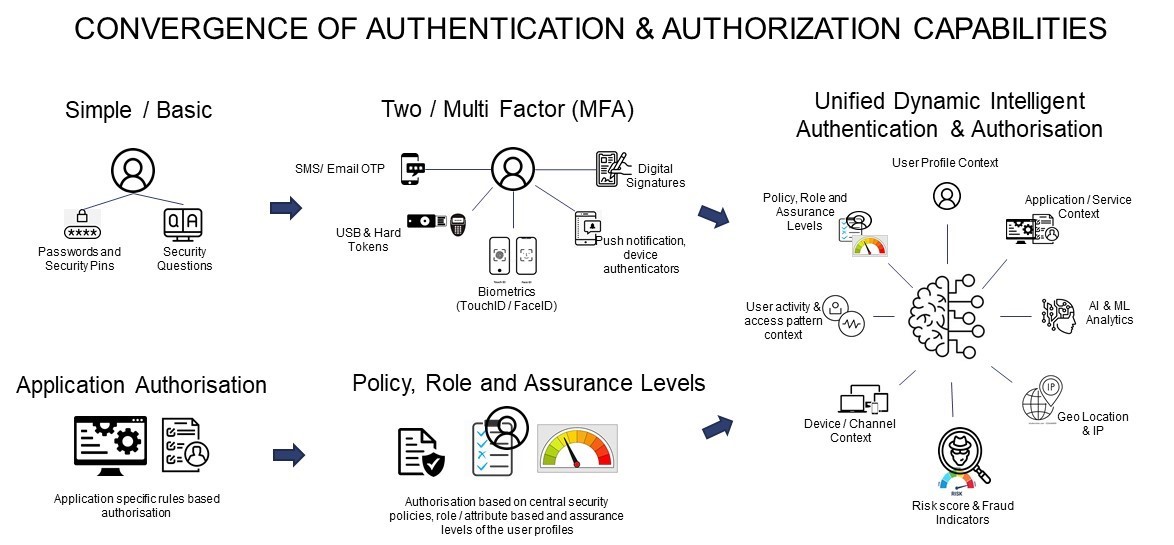
The authentication and authorization capabilities are evolving and converging to form a unified dynamic intelligent service provided to the users based on the context of the services they use and the risk to the assets they are trying to access. A study by Verizon in 2022 described that almost 80% of cyber-attacks are due to stolen or weak passwords. Hence there is a clear initiative by businesses and organisations to move away/shift from password-based authentication to password-less solutions.
Moreover, there are standards that are also evolving in this space to ensure and help organisations and solution providers in this area to move and adapt to offer these capabilities, for example, the FIDO (Fast Identity Online) by the Kantara Initiative and FIDO Alliance. Tech Giants like Apple, Microsoft, and Google have already announced on World Password Day on 5th May 2022 that they are all committed to implementing password-less authentication across mobile, desktop, and browser platforms.
Multifactor Authentication (MFA) is also evolving to be adaptive, MFA powered by AI-based security approach considers the user’s behavior and context that he/she is operating in while using the digital services. AI introduces a heuristic or behavioral approach to identify unusual patterns and introduces additional factors of authentication based on the user’s context while he/she is navigating through the digital services provided by organisations.
It is encouraging to observe that more and more organisations are considering and investing to mitigate the weaknesses in their organisation’s authentication methods. It is expected that in the post-pandemic era, there will be a gradual shift towards using unified intelligent authentication features and capabilities that enable adaptive and password-less MFA.
Though these capabilities are undoubtedly more secure than credential-based authentication, organisations still need to implement them intelligently/carefully to have the desired outcome towards reduced cyber-attacks and incidents.
Digital security and privacy are forming the foundations of the new Internet security architectures. Cyber criminals are making tasks increasingly difficult with sophisticated threats and technologies and the hope for organisations is that authentication services in digital security are always at the forefront and a step ahead to counter these threats.
To learn more, please reach out to our experts Denise Walker (denise.walker@mastek.com) and Rashi Malhotra (rashi.malhotra@mastek.com).
.png?width=100&height=100&name=MicrosoftTeams-image%20(16).png)